Web applications are not static sites but a careful composition of static and dynamic content. More common than not, the web application logic runs in the browser. Instead of fetching all content from the server, the application
- Home
- Author: frontend
Ready to give Turbopack a try? Once upon a time in web development, building web pages required just HTML, CSS, and some JavaScript for interactivity. However, as projects grew in scale and complexity, the need for efficient
Hey everyone! If you're a fan of Next.js like I am, you'll be excited to know that Next.js 15 is here and packed with fantastic new features and improvements. Whether you're a seasoned developer or just getting
Why Strapi is the Go-To Solution for Modern Content Management In the rapidly evolving digital landscape, managing content effectively has become a cornerstone for businesses aiming to provide seamless and engaging user experiences. Traditional Content Management Systems
React.js has been one of the most popular JavaScript libraries for building user interfaces, and with good reason. Its component-based architecture, rich ecosystem, and scalability make it the go-to choice for developers worldwide. But mastering React goes
Let's set the stage with a cliché: software development is constantly evolving towards ever higher levels of abstraction. We have object-oriented and functional programming built on top of imperative programming on top of assembler on top of
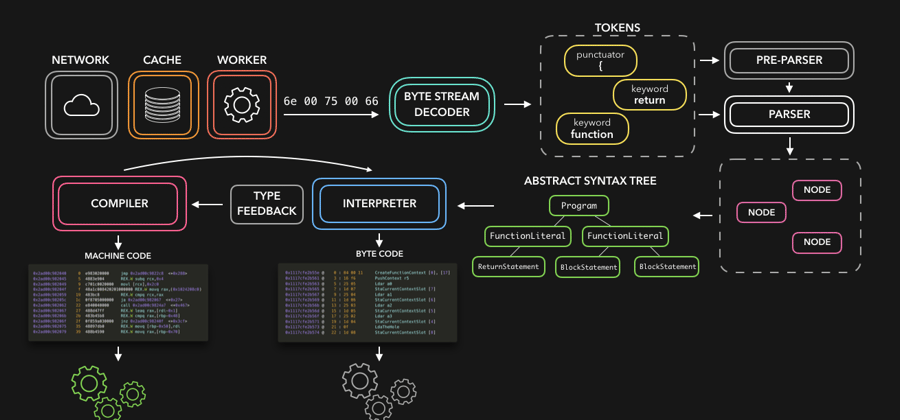
JavaScript is cool (don't @ me), but how can a machine actually understand the code you've written? As JavaScript devs, we usually don't have to deal with compilers ourselves. However, it's definitely good to know the basics of the
The Evolution of Signals in JavaScript: A Path Towards Fine-Grained Reactivity In the ever-evolving landscape of frontend development, state management has always been a focal point of innovation. From the early days of managing state with simple
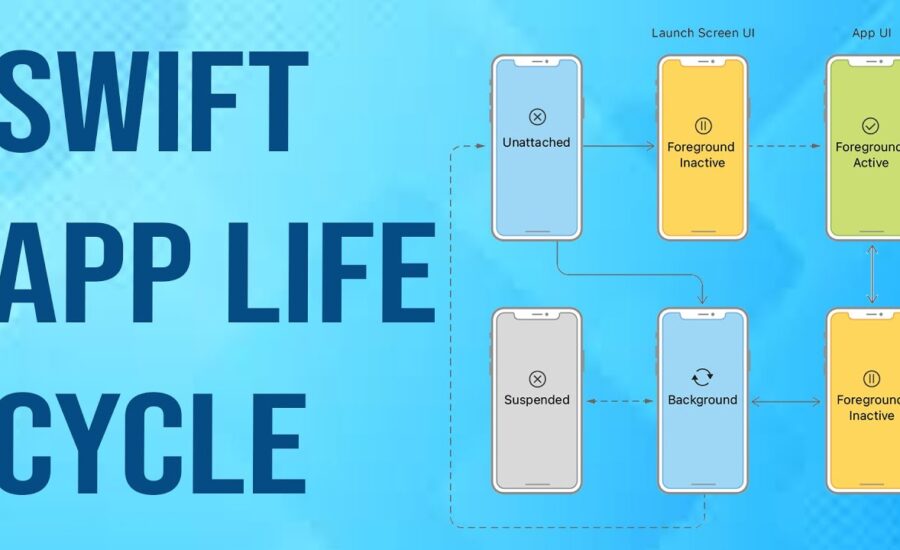
With this in-depth guide, learn how to implement SwiftUI and manage your app’s life cycle effectively. Discover the best practices and techniques to take your iOS app development to the next level. When you are using an
We have all experienced it: starting is the toughest part of any journey. So getting started in the ML field wouldn’t be any different. This is why today I want to highlight some of the essential tools